In PaperCut it’s possible to synchronize users from more than one source such as Active Directory and LDAP or G-Suite, or even with multiple Active Directory domains. Synchronizing with multiple Active Directory domains is possible, and this article exists to showcase those options and provide an outline of the steps for each.
When needing to sync users from two or more Active Directory domains, or adding a second domain, these are the options:
- Have a trust between domains. Make sure PaperCut is running as a service account with rights to query each of the domains.
- Set up a secondary sync source in PaperCut with the LDAP connector and point to the other Active Directory domain.
Option 1 - Trust between domains
If your organization already has configured a trust between domains, then this is something that you can leverage with PaperCut.
Steps:
-
Set up PaperCut to run as a Service Account with rights to query all of the domains.
-
Log in to the web interface of your PaperCut server as an administrator.
-
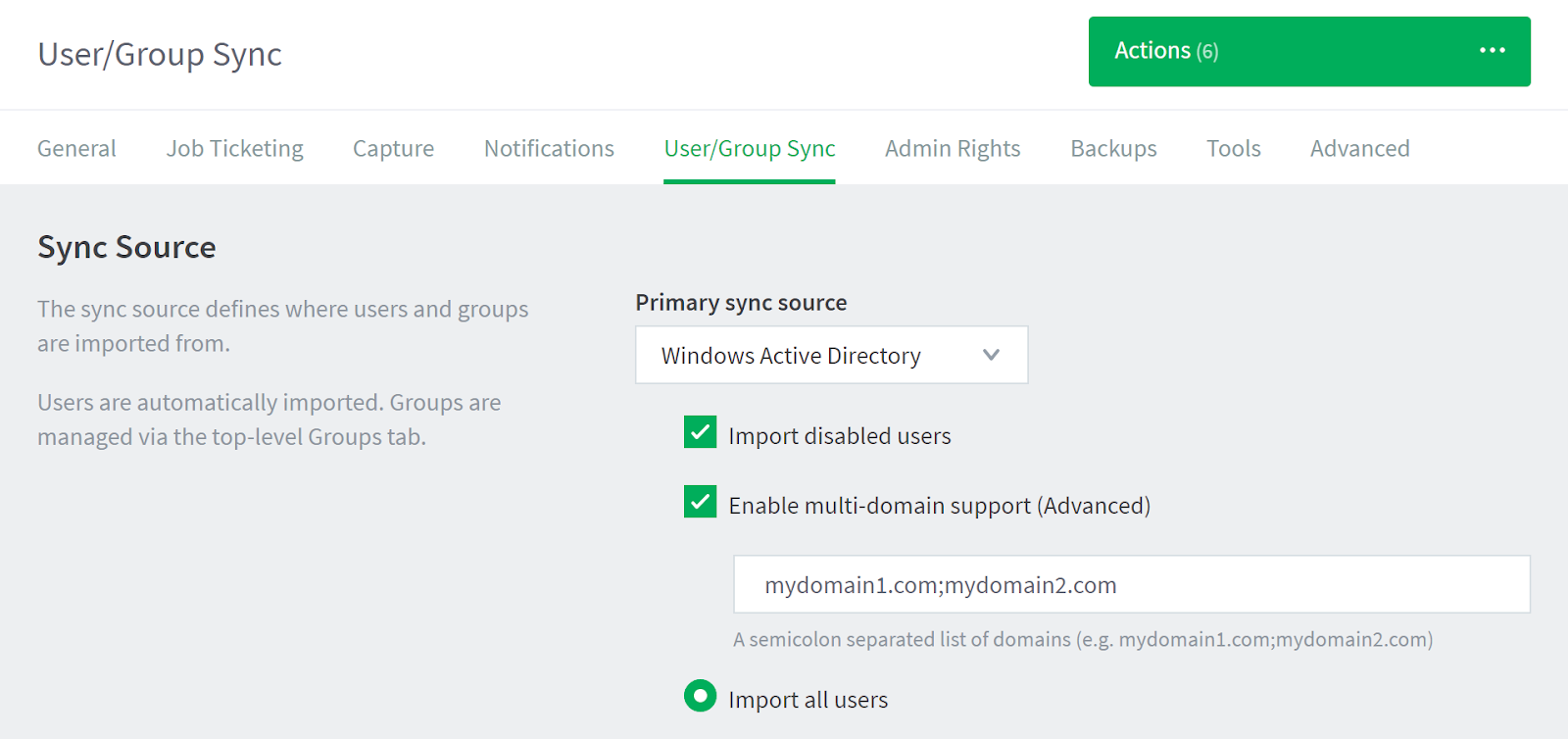
Navigate to the User/Group Sync tab.
-
Check the box Enable multi-domain support (Advanced).
-
Enter a semicolon-separated list of the domains in your Forest (up to 20) that you would like to synchronize users from.
-
Click Test Sync Settings to confirm that the right users will be imported.
-
Click Apply and Synchronize Now when finished.
One customer who was attempting to set up PaperCut to sync with two domains that were in different forests had configured a trust between the two forests, but the sync was still failing with the error “User directory encountered error running command… User directory command returned status −2147217865.”. In troubleshooting they discovered that a firewall was blocking TCP and UDP port 88 which appears to be required for User and Computer Authentication and Forest Level Trusts. Once the port was unblocked, the sync completed successfully.
Option 2 - use LDAP for the second domain
If the first option doesn’t work for whatever reason, then there’s another method to get users imported from another Active Directory domain, but there are a couple of limitations. The downsides to this method are that it will only work with one additional domain, and it will not support nested groups.
Steps:
-
Log in to the web interface of your PaperCut server as an administrator.
-
Navigate to the User/Group Sync tab.
-
Scroll down to Secondary Sync Source and check the box Enable secondary sync source.
-
Then for the LDAP Server Type choose Active Directory, and fill out the remaining fields with the correct details for your domain.
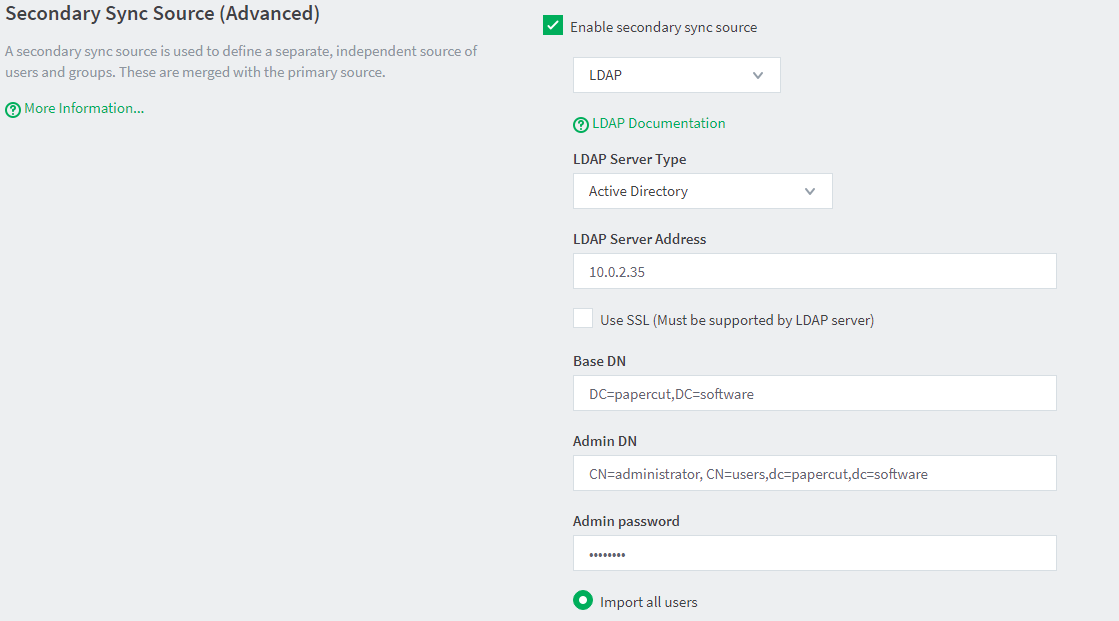
- LDAP Server Address - this can be the IP or Hostname of your Domain Controller.
- Base DN - the path to where your users live, This could be the entire domain (assuming the domain is papercut.software): DC=papercut, DC=software. or if you wanted to filter it down and only include users from a certain group or OU you could use: CN=Users,DC=papercut,DC=software. For an OU it would be: OU=print-users, DC=papercut, DC=software.
- Admin DN - the full distinguished name for the user. The default administrator account would be: CN=Administrator,CN=Users,DC=papercut,DC=software. To find this if you go to View > Advanced Features in “Active Directory Users and Computers” then find the user you want to use and right click > properties and select “Attribute Editor” you will see a list of the attributes including “distinguishedName”. Or if you want to use PowerShell, run Get-ADUser [username] which will output the distinguished name and other fields.
- Admin password - the password for the above administrator account.
-
Click Test Sync Settings to confirm that the right users will be imported.
-
Click Apply and Synchronize Now when finished.
What if the same username exists in both domains?
By default, if PaperCut comes across two or more users with the same username during a sync, they will be merged into a single user account. However, it is possible prevent this from occurring by configuring PaperCut to synchronize the User Principal Name (UPN) instead. To do so, follow the instructions in Prevent username clashes in Windows multi-domain environments.






Comments