When is printing not a nightmare? Many sysadmins and IT teams struggle with printers daily. But this particular Windows print spooler vulnerability causes a lot of bad dreams.
It’s a bug that means a domain user (once they’ve been authenticated against the remote system) can remotely run code on a Microsoft Windows system as the local SYSTEM user.
Both the exploit and the subsequent patches and fixes from Microsoft are referred to as “PrintNightmare".
It’s also known by its official code titles CVE-2021–1675, CVE-2021–34527, and CVE-2021–34481.
PrintNightmare vulnerability: background on the Windows spooler exploit
In June 2021, security researcher Zhiniang Peng tweeted a proof of concept exploit. It contained an unpatched zero-day vulnerability in all supported and Extended Security Update versions of Windows OS.
Despite immediately deleting the Tweet, the exploit was quickly all over GitHub. To make matters worse, Windows’ latest June 2021 security pitches didn’t fix the exploit. This was the beginning of the nightmare part.
Despite Windows fixing the print spooler vulnerability, that fix initially didn’t make its way into their security patch. It was initially tagged as CVE-20201-1675 but on 21 June 2021 Microsoft upped the severity of the vulnerability to Remote Code Execution.
Listen to the Print Geeks podcast for more on PrintNightmare.
Technical explanation: why is PrintNightmare a print nightmare?
The exploit exists within the RpcAddPrinterdriver. This exists to enable remote printing and driver installation. It’s a necessary function that entrusts IT admins with SeLoadDriverPrivilege. This provides the ability to install new printer drivers to a remote print spooler.
Essentially, this becomes an exploit because it means any “authenticated” user, not just the trusted, permitted sysadmins, can add any ‘Print Driver’ to Windows.
Any random user can escalate this privilege to become a domain admin. Then, if they’re a malicious actor, start causing chaos with some nasty code.
Microsoft fixed the exploit, as a result, they were constantly changing the defaults for Windows Point and Print. The complication with Point and Print was, as a connection to a printer shared from a server with Type 3 drivers, the Print Driver (software) gets downloaded from the server onto the client machine.
Fixing the exploit meant changing the rules for Point and Print, which had some dire side effects for a lot of Windows print environments.
The new rule Microsoft has created for Point and Print is you now have to be an administrator/have administrative access on your client machine in order to install the Print Driver from the print server. Another new default they introduced was, if you’re not on Windows, you can’t connect to a Windows shared printer.
To sum all that up, Microsoft addressed the exploit pretty early on with their patches. The impact/nightmare of the situation was the fallout from Microsoft fixing the vulnerability due to how it impacted Point and Print.
How to fix PrintNightmare | Understanding the Microsoft patches
Stopping the print spooler service is a quick solution, but unrealistic because that will also stop printing.
The easy answer is: patch your Windows systems. Because the nightmare’s over, Windows fixed the exploit. But you’ll need to do your homework first.
There are multiple patches from Microsoft available via Windows Updates, and links in the Microsoft Advisory on the exploit.
The smartest thing to do is read the Microsoft Advisory in full. Assess the risk PrintNightmare poses to your systems. Then understand the impact and scope of all the mitigation options before you take action.
We recommend you patch any system exposed to the Microsoft Windows print spooler. And in order to stay fixed, you need to keep running the security updates from Microsoft.
How PaperCut solved PrintNightmare
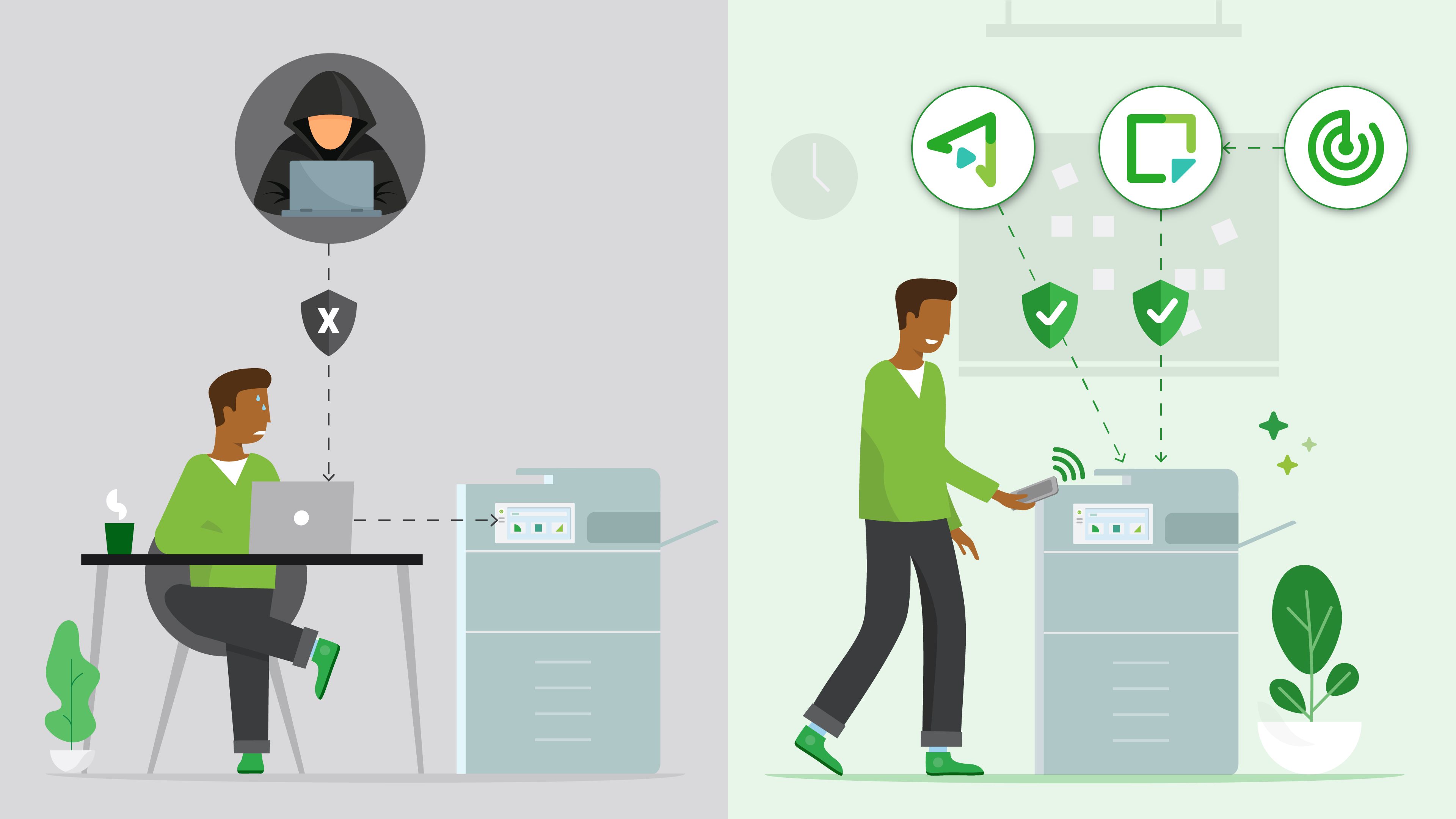
If you need another solution instead of Windows Point and Print, PaperCut’s solution Mobility Print delivered with Print Deploy (available with PaperCut MF) is a suitable alternative for Windows Point and Print.
Stated simply, those new Point and Print rules don’t apply to PaperCut. Print Deploy can install a client, without admin access, and the Mobility Print printer can be delivered to the client machines.
With a few extra steps, Print Deploy can also deliver the vendor driver onto the client machine, for those end-users who need higher functionality options. You can also deliver that printer to specific groups, or your whole organization.
Learn more about PrintNightmare:
We have a Knowledge Base article on how PaperCut is impacted and all the recommended workarounds.
To find out how Mobility Print and Print Deploy provide an alternative, check out our blog article: 4 ways to fix PrintNightmare with PaperCut.
We also talked about PrintNightmare on our podcast, Print Geeks. PaperCutter Alan Morris actually worked on Windows printing during his days at Microsoft, and shares some behind-the-scenes insights.
Want to stay in the loop on all things printing?

Subscribe to PaperCut's newsletter
We'll make sure you know what's happening in the print world, as well as tips and tricks to make printing less of a headache.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.