The hybrid workplace is rising. The office is changing, and printing is changing too.
Users used to primarily press print onsite, at their desks, but we’re now in the hybrid working era. Users print from different locations and devices every day, meaning that your print security needs to evolve and adapt.
That’s why more organizations are adopting a zero-trust approach for their security, including print.
Print security is frequently overlooked and underestimated by many organizations. Mainly because cybersecurity monopolizes all the news ink. But your printing environment is both a physical and cyber link in your overall security chain.
Protecting your printing is a crucial part of protecting your data, systems, and physical information from cyberattacks and security leaks.
Understanding the basics of print security
Printers are often seen as harmless peripheral devices, but they’re more than a big grey box you use to print cat pictures.
Business printers store, process, and transmit highly sensitive data and convert them into physical objects – invoices, orders, contracts, and agreements. These contain sensitive information like financial and personal data, which are appealing targets to cybercriminals.
Printers can be hacked and used to access your network, data, and systems, or to launch malware or ransomware attacks.
But they’re also potentially harmful in the wrong hands within your organization.
That sounds melodramatic, and we’re not suggesting you should suspect all users in your network of nefarious intent. But something like a misplaced or forgotten document can create huge security risks.
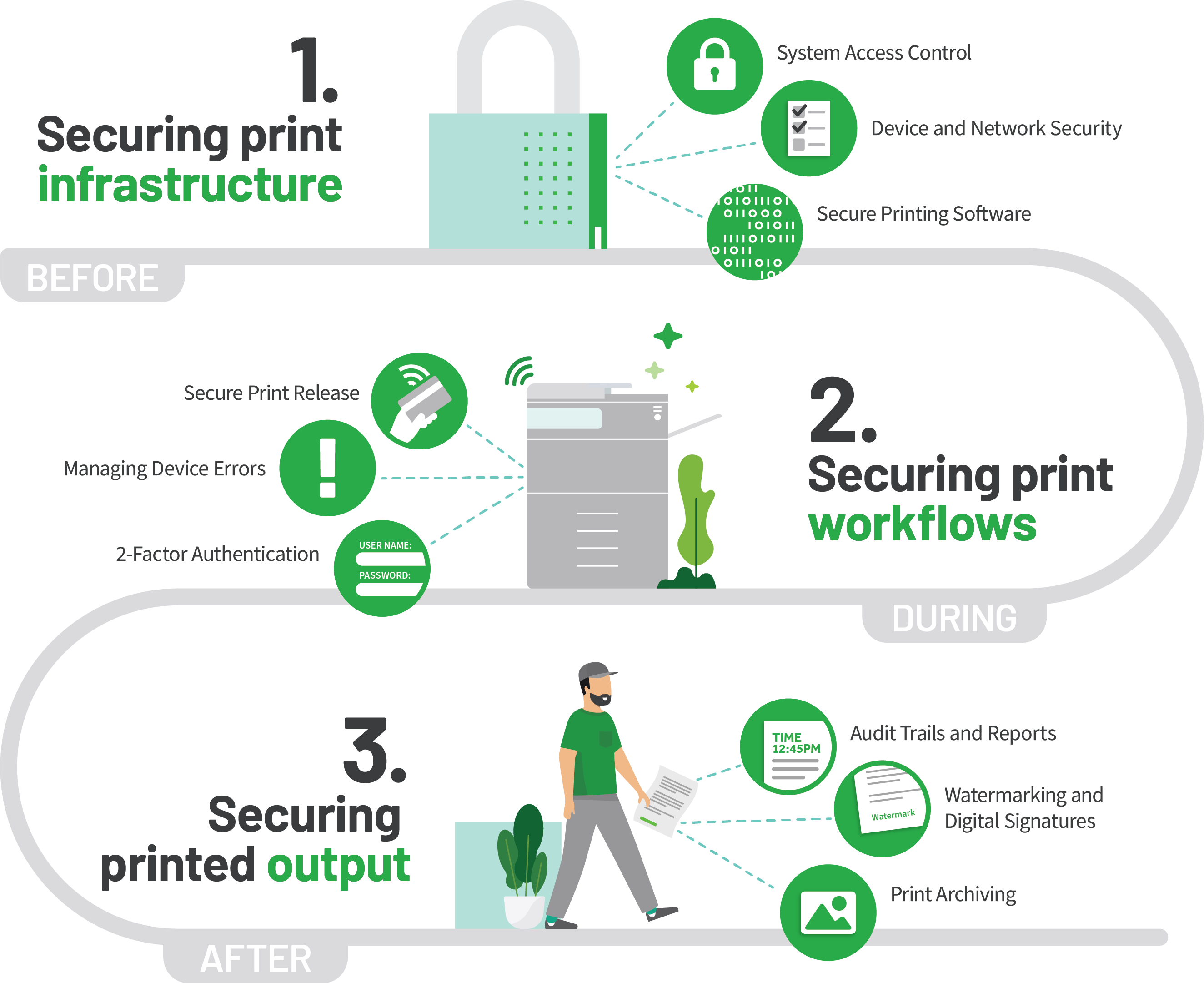
There are a lot of security elements in play when you press print. Print security is a Venn diagram of physical, technical, and procedural fault points. Securing your printing means securing your print devices, print data, and print documents from unauthorized access.
You need to secure the physical printers and devices, protect the sovereignty of your data in transit and in motion, and secure your personnel and workflows.
Little did you know, hitting CTRL+P on your keyboard could be the weakest link in your organization’s security posture – securing your printing means securing three areas of your print environment:
Print devices
Updating firmware, disabling unused ports and protocols, enforcing authentication (e.g. 2FA or MFA) and encryption, and applying patches and updates.
Print documents
Implementing secure printing features, watermarking or digital signatures, and deleting print jobs after completion.
Print network
Securing your print infrastructure, segmenting your network, using firewalls and VPNs, and monitoring and auditing print activity.
The principles of zero-trust printing
More and more organizations are adopting zero-trust security principles for their business technologies, and printing is a part of that picture.
The zero-trust security model assumes that no device or connection is trusted by default. Just because you authenticated this morning when you pressed print, doesn’t mean you don’t have to authenticate later in the day.
Instead of relying on a traditional network perimeter to protect your resources, a zero-trust approach verifies every connection and request before granting access. This way, you can prevent unauthorized access and contain breaches if they occur.
A zero-trust approach is especially relevant for print security in the hybrid workplace, where users print from different locations and devices. Traditional network-based security may not be sufficient or applicable for remote or mobile printing scenarios.
Adopting zero-trust principles like an “always verify” approach can help you secure your print environment regardless of where your users are printing from or what devices they are using.
Identifying potential vulnerabilities
Before implementing a zero-trust printing policy, you need to identify the potential vulnerabilities in your print environment:
- Unsecured printers: No passwords or access control, no or late firmware updates.
- Unsecured print data: No encryption.
- Unsecured print network: No network segmentation, no firewalls or VPNs.
- Unsecured print users: No user authentication or authorization.
- Unsecured print devices: Unmanaged or not updated printers/copiers.
Developing a print security policy
To address these vulnerabilities and implement a zero-trust printing policy, you need to develop a comprehensive print security policy:
- Device security: Apply firmware updates, disable unused ports and protocols, enforce authentication and encryption, and apply patches and updates.
- Data security: Implement secure printing features like PIN codes or pull printing, watermarking/digital signatures , and deleting print jobs after completion.
- Network security: Segment your network, use firewalls and VPNs, monitor and audit print activity.
- User security: Verify every user and device before allowing print data access.
Training employees
The first step of security is education. The weakest link in the security chain is human error. That’s not being judgmental. We’re all capable of mistakes. We’re all flawed. It’s just that sometimes those slip-ups are significant security risks.
There should be guardrails in place for when things get a bit wobbly. The best way to even just reduce security issues is by training and teaching your workforce in the nuances of print security.
Once secure printing features are implemented, users need to be taught how to use them effectively. Organizations should also communicate why secure printing features are being used.
Especially when some secure printing practises can be seen as inconvenient and inefficient.
Monitoring and auditing
Just because you’ve pressed print and collected your document, doesn’t mean that print job ceases to exist as a cog in the security wheel.
Your administrators still need visibility of print data and output for security purposes. Monitoring and auditing with print management software makes all print transactions detectable and recoverable.
By keeping an eye on your print environment, and enforcing accountability, your system administrators can detect and prevent any unauthorized or malicious print activity.
They can also identify leaks to plug up with more security features, or by hardening existing processes and procedures. This is why print management software is fundamental to securing your print environment.
The future of print security
Print security is not a one-time event. It’s an ongoing process that requires constant vigilance and adaptation. As the hybrid working reality and modern working world mutates and shifts, print security evolves alongside it.
Adopting zero-trust principles for your print environment can help you secure your printing regardless of where your users are printing from or what devices they are using.
However, zero-trust isn’t a magic security cure-all that means you’ll never have any security leaks and never have to mitigate a security risk ever again.
Zero-trust means your business technologies follow a design framework where access to resources is constantly scrutinized. Access is always verified, no matter who is printing, or how frequently.
Let us help you make sure your printing is secure
Our team of experts can help you choose the right print management solution to simplify how you print – chat to us today to learn more about how PaperCut can help you print simply and securely.

Speak with Sales
Need a little help from a human? Speak with us, we don’t bite.
By filling out and submitting this form, you agree that you have read our Privacy Policy, and agree to PaperCut handling your data in accordance with its terms.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.